Top 5 Benefits of End-to-End Encryption in Your Business

If your business relies on digital communication—and these days, whose doesn’t?—you’ve probably noticed how quickly privacy concerns have become part of daily operations. Data leaks no longer make headlines because they’re rare; they make headlines because they happen constantly. A single exposed chat thread, misdirected file, or compromised meeting link can trigger days of reputational damage, financial fallout, and messy investigations.
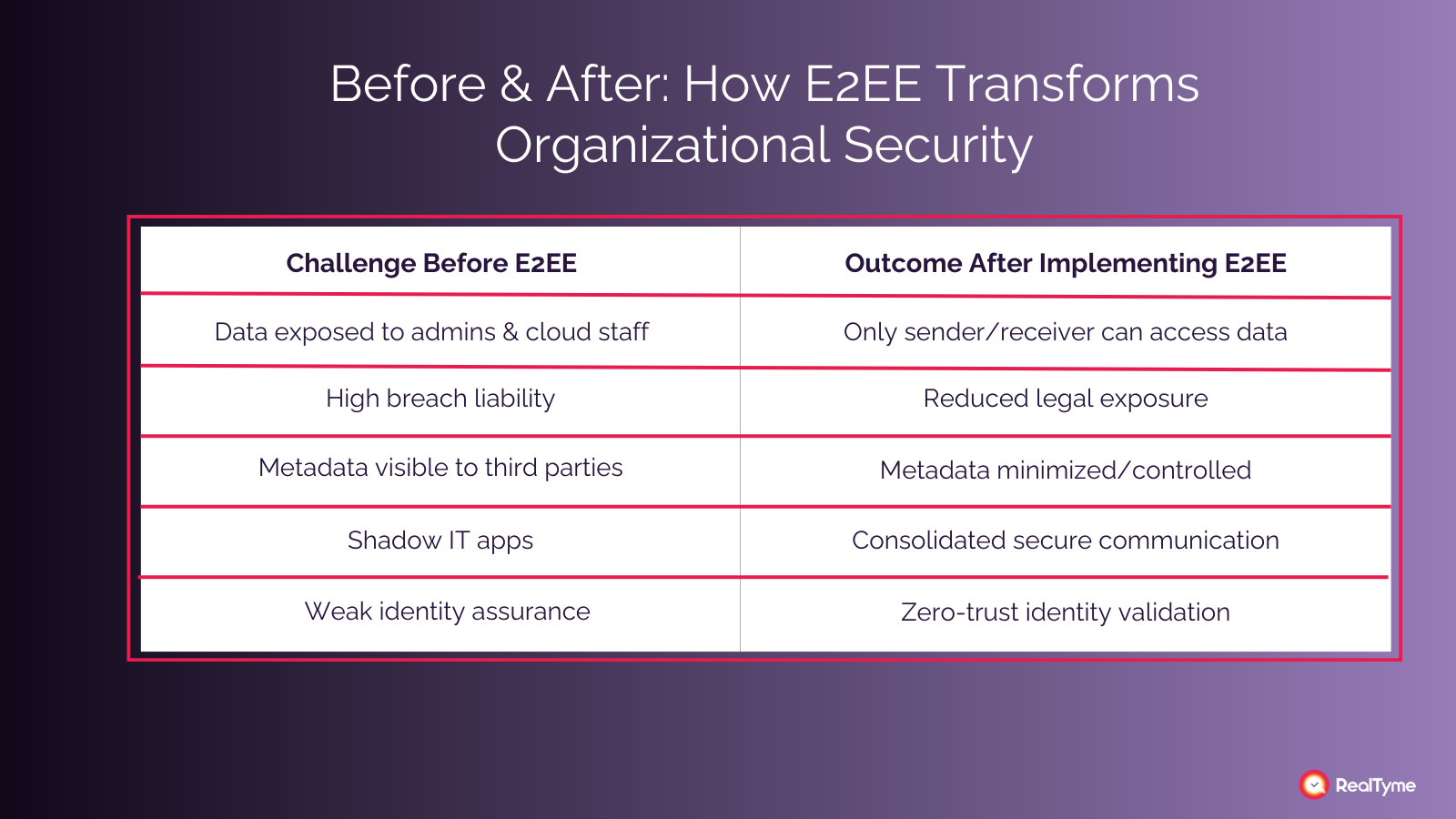
End-to-end encryption (E2EE) has become the closest thing to a guarantee that your information stays where it belongs. Still, many companies think encryption is something their IT team “already takes care of.” And while that may be true in part, the reality is that not all encryption is equal—and not all collaboration tools treat your data the same way.
Consumer messaging apps like Signal or WhatsApp are great examples of E2EE done well—but they’re built for private conversations, not organizational-level operations. Meanwhile, workplace tools like Microsoft Teams or Slack offer layers of protection but are not designed as true end-to-end encrypted environments by default, especially for files, metadata, or administrator access.
That’s where platforms like RealTyme stand apart: engineered specifically for business-grade secure communication, private team collaboration, and minimal data exposure—without compromising usability or productivity.
In this article, we’ll break down the top five reasons why businesses should adopt end-to-end encryption, what problems it actually solves, and why RealTyme has emerged as the most reliable platform for organizations who want to move forward without putting sensitive information at risk.
.png)
1. Stronger Data Protection and True Confidentiality
Many companies think encryption simply means “scrambled data.” But the crucial difference with end-to-end encryption is control. With E2EE, only the sender and the recipient hold the necessary keys to view the message. No one in the middle—not the service provider, not cloud administrators, not even the platform itself—can unlock the content.
This is where typical business tools fall short. While Microsoft Teams, Google Workspace, and many cloud-based systems encrypt data at rest and in transit, they still technically have the ability to access the information stored on their servers. It’s not that these companies misuse data, but having the ability means the data becomes a target.
Attackers know this. That’s why cloud environments, no matter how reputable, are frequent points of attack.
With true end-to-end encryption:
- A compromised server can’t reveal anything.
- An intercepted message appears as useless noise.
- Administrators can manage accounts without ever seeing message content.
- Your organization doesn’t rely on “trusting” a third party—only on math.
This matters enormously for industries handling deeply sensitive data: healthcare, legal, financial services, defense, manufacturing, research, or any team dealing with proprietary workflows.
RealTyme takes this even further by fully limiting metadata exposure and ensuring the platform cannot read or access communication. Everything from calls to messages to shared documents is encrypted on the user’s device before leaving it, making the risk of interception dramatically smaller.
In short, E2EE turns confidentiality into a dependable operational foundation, not just a technical feature.
2. Increased Customer Trust and A Stronger Brand Reputation
Trust is not built through marketing anymore. It’s built through behavior, transparency, and your ability to protect people’s data.
When a customer interacts with your business—whether booking an appointment, sharing financial details, or simply exchanging messages—they’re evaluating you every time. They want to know: If I share this information, will it remain confidential?
Companies that adopt end-to-end encryption send a clear message:
Your privacy is non-negotiable.
And that message creates something extremely valuable—loyalty.
Today’s customers are much better informed than they were even five years ago. They understand data breaches. They know about phishing and stolen credentials. They’ve seen tech giants mishandle personal information. Many have had their own accounts hacked or identities stolen at some point.
This heightened awareness means people actively look for businesses that prioritize security.
RealTyme helps companies communicate that commitment effectively. Unlike consumer messaging apps—which are made for daily conversations, not compliance-driven workflows—RealTyme offers private spaces where teams and clients can exchange information without worrying about leaks or backend access.
This is especially helpful for:
- Lawyers sharing case files with clients
- Doctors discussing treatment plans
- Financial advisors exchanging account information
- Consultants handling confidential strategies
- Startups protecting intellectual property
- Executives managing high-stakes deals
While Signal or WhatsApp offer great private E2EE messaging for personal use, they lack enterprise controls, governance tools, and the organizational structure companies rely on.
When clients see you’re using a platform like RealTyme—which blends true security with professional collaboration—they instantly understand your commitment to protecting their data. That’s a competitive advantage no marketing budget can buy.
Simply put: strong privacy practices don’t just prevent problems, but they strengthen how customers perceive your brand.
3. Better Compliance and Reduced Legal Risk
Regulations around data privacy have changed dramatically in the last decade. Whether your organization operates in Europe, the U.S., the Middle East, or globally, one thing is universal: violations are expensive.
Laws like GDPR, HIPAA, PCI-DSS, the California Privacy Rights Act, or even sector-specific rules in finance and government require companies to safeguard sensitive data. And if there’s an incident, the question regulators ask first is:
Were reasonable security measures in place?
End-to-end encryption is one of the clearest, most defensible answers you can give.
E2EE not only protects data during transmission, but it also limits the number of people who can theoretically access it. Traditional communication systems create several points of vulnerability:
- Cloud storage
- Internal servers
- Administrator dashboards
- Backup repositories
- Vendor-managed systems
Every one of these points is a potential compliance headache.
With platforms like RealTyme, those vulnerabilities shrink significantly. The platform is designed so neither RealTyme nor your IT administrators can decrypt or view user content. Only the intended parties can.
This reduces:
- Privacy violation risks
- Liability during audits
- The scope of compliance reporting
- Legal exposure if a breach occurs
- The number of attack surfaces organizations must guard
Additionally, RealTyme can be deployed in a private, isolated, or on-premise environment—giving organizations full sovereignty over their communication infrastructure. This is crucial in industries such as public sector, healthcare, manufacturing, or research, where cloud-dependency is a major concern.
In essence, a secure architecture makes compliance not just achievable but sustainable.
4. Protection Against Insider Threats, Cloud Breaches, and Alignment With Zero-Trust Principles
Most cybersecurity discussions traditionally focus on external hackers, but modern breach reports show a very different reality: a large percentage of incidents originate from inside the organization. Some are intentional—employees misusing access or leaking information. Many are accidental—someone forwarding a confidential file to the wrong group, syncing documents to a personal device, or leaving a laptop unlocked.
Until a few years ago, these internal risks were the main concern. But today, there’s a new dimension: AI-powered attacks that can analyze massive amounts of exposed data, predict user behavior, impersonate individuals, and automate targeted exploitation at a scale impossible for human attackers.
This is where traditional collaboration platforms, especially those with broad administrator access or exposed cloud metadata, become vulnerable. If an AI-driven threat actor gains access to even small slices of corporate data, they can rapidly infer patterns, reconstruct conversations, or craft highly convincing social engineering attempts.
End-to-end encryption removes this opportunity entirely: even if communication is intercepted or a system is breached, the attacker—human or AI—has nothing meaningful to analyze.
And this is exactly why modern cybersecurity frameworks rely on the Zero-Trust model.
Zero-Trust: A Security Approach Made for the AI Era
Zero-Trust is often oversimplified as “trust nothing.” The real principle is more practical:
Do not assume anyone—inside or outside your network—is trustworthy by default. Every access request must be verified and minimized.
In a world where AI can automate credential stuffing, generate perfect phishing messages, or simulate internal communications, Zero-Trust has become essential. It includes:
- Least-privilege access: users only see what they absolutely need.
- Continuous verification: devices, identities, and connections are checked constantly.
- Micro-segmentation: systems are divided into isolated compartments.
- No implicit trust: internal network traffic is treated as risky by default.
AI-assisted attacks thrive on visibility, volume, and poorly segmented systems. Zero-Trust minimizes the “surface area” they can exploit.
How End-to-End Encryption Neutralizes AI Threats
AI attacks succeed because they process vast amounts of data to find weaknesses.
E2EE cuts them off at the source. It ensures:
- AI cannot analyze content it can’t see
Intercepted data is meaningless without decryption keys.
- Compromised cloud environments don’t expose readable messages
Even if an AI system scans server logs or intercepted traffic, it finds only ciphertext.
- Admins can’t over-access data, limiting insider misuse or exploitation
AI-driven privilege escalation attacks often target admin accounts. E2EE weakens this strategy because admins cannot decrypt anything.
- Reduced metadata exposure minimizes pattern inference
AI excels at understanding patterns. RealTyme limits metadata to prevent this.
This is a key distinction between platforms. Consumer messaging apps like Signal and WhatsApp provide E2EE, but lack enterprise policies, governance structures, deployment control, and metadata reduction—all essential for protecting organizations against AI-assisted reconnaissance.
Why RealTyme Is Uniquely Designed for Zero-Trust + AI-Safe Communication
RealTyme doesn’t just use E2EE. It builds the entire platform around the idea that no one should have unnecessary access. That’s the heart of Zero-Trust.
RealTyme offers:
- True end-to-end encryption for messages, calls, files, and workspaces
- No backend decryption capability — not even by RealTyme
- Minimal, tightly controlled metadata
- Private/on-premise deployment options, avoiding Big Tech cloud exposure
- Role-based access, compartmentalized workspaces, and isolated environments
- Strict separation of teams and projects to reduce internal blast radius
- Infrastructure that AI reconnaissance tools cannot analyze or map
RealTyme enables Zero-Trust communication without adding friction to everyday work, something mainstream tools simply weren’t designed for.
Real-World Incidents That Prove End-to-End Encryption Alone Is Not Enough
End-to-end encryption protects message content, but recent incidents show that organizations face threats that go far beyond simple interception. Many high-profile breaches in the past few years didn’t crack encryption—they exploited everything around it: metadata, identity spoofing, platform weaknesses, and cloud ecosystems that collect more information than most people realize.
Here are a few examples that exposed the limitations of many mainstream platforms:
1. WhatsApp’s Massive Metadata Exposure — 3.5 Billion Phone Numbers Leaked
While WhatsApp encrypts messages, its platform still exposed a vast scrape of 3.5 billion phone numbers and profile photos. The content remained encrypted, but the metadata—who uses the app, when, and with what identifiers—was enough to create real privacy and security concerns.
This incident revealed a harsh truth: E2EE cannot compensate for a platform that collects large amounts of identifiable metadata.
2. Microsoft Teams and “Hybrid Work Transparency” Tracking
Microsoft introduced workplace analytics features marketed as insight tools for hybrid work. But for employees, it felt uncomfortably close to internal surveillance.
Although Teams is widely used for business communication, it relies heavily on cloud analytics, usage tracking, and server-side visibility, which creates unnecessary internal and external attack surfaces.
Even with encryption layers, the system architecture itself invites risks.
3. The Signal Clone That Compromised Government Communication Channels
A cloned, malicious version of Signal circulated in certain regions and successfully tricked officials into using it. The incident exposed how vulnerable organizations can be when relying on consumer apps not designed for controlled deployment or workspace governance.
4. “Marco Rubio” and the Diplomatic Deepfake Incident
In a widely discussed diplomatic case, a foreign official was contacted by what appeared to be U.S. Senator Marco Rubio—but it was a sophisticated deepfake impersonation designed to manipulate international communication.
This was a failure of identity validation, authentication, and Zero-Trust architecture.
What these incidents teach us
All four cases point to a single conclusion:
Encryption protects your messages, but it cannot protect your organization from the weaknesses of the platform itself.
- Metadata can still leak
- Identities can be spoofed
- Cloud providers can still access analytics
- Compromised apps can bypass security
- AI-driven threats can exploit patterns and impersonate people
This is why businesses need more than “an app with end-to-end encryption.”
They need:
-Minimal metadata exposure
- Strong identity assurance
- Zero-Trust environments
- Private or isolated deployments
- No cloud surveillance
- No vendor visibility
- No analytics engines watching their teams
- Strict separation of internal communication spaces
This is exactly where RealTyme stands apart from mainstream messaging platforms.
5. Secure Remote Collaboration and Future-Proof Operations
Remote work has evolved from a temporary necessity into a standard mode of business. Teams collaborate across borders, contractors access shared files, executives communicate from airports, and clients expect instant responses regardless of time zones.
But while remote work boosts productivity, it also magnifies risk. Public Wi-Fi, personal devices, home networks, and shared computers all increase the chance of data exposure.
End-to-end encryption creates a foundation where remote communication feels as secure as in-person conversations inside a private office.
RealTyme strengthens this foundation by integrating secure messaging, calling, file-sharing, and teamwork spaces—all in an encrypted environment that can be deployed privately. Nothing is processed through advertising systems, data mining engines, or analytics platforms. There are no profiling practices or hidden access points.
This allows organizations to:
- Collaborate without worrying about third-party exposure
- Share files even when traveling or on unfamiliar networks
- Conduct private meetings with guaranteed confidentiality
- Work with international teams without compliance concerns
- Build communication systems that scale as the business grows
Future-proofing communication isn't about predicting threats—it's about reducing the number of things that can go wrong. And that's where RealTyme excels.
How to Implement End-to-End Encryption in Your Organization
Transitioning to an E2EE environment is easier than most companies expect. The key is to approach it strategically rather than reactively.
1. Assess your current communication tools
List what apps teams use daily—chat platforms, email, file-sharing tools, meeting apps. Identify which apps handle sensitive data.
2. Identify risk areas
Common weak points include:
- Unencrypted backups
- Personal messaging apps used for business
- Cloud drives shared across departments
- Email attachments
- Ad-hoc collaboration tools
3. Choose a platform designed for business E2EE
RealTyme is built specifically for organizations that need more than secure texting:
-Encrypted collaboration hubs
- Controlled workspaces
- Secure meeting tools
- Private communication channels
- Self-hosted deployment options
4. Train your teams
Introduce best practices such as secure password management, recognizing phishing attempts, and proper device handling.
5. Set up internal policies
Define how employees share files, store documents, and communicate with clients.
6. Audit regularly
Security systems are strongest when maintained. Ensure tools are updated, access rights are current, and new hires receive proper onboarding.
By following these steps, organizations can smoothly move into a communication environment that protects both people and information.
Conclusion
Businesses operate in a climate where a single leaked message can undermine years of work, a mishandled file can trigger regulatory fines, and a compromised account can expose entire projects.
End-to-end encryption offers a clear path toward safer, more reliable collaboration. It protects confidentiality, builds trust, strengthens compliance, minimizes internal risk, and prepares organizations for the future of remote and global work.
Consumer apps like Signal and WhatsApp have shown the world the value of E2EE—but platforms like RealTyme bring that level of protection into the professional realm, with structure, governance, and enterprise-grade control.
For businesses that treat communication as an asset—not a liability—RealTyme is the right way forward. Get started with RealTyme today or schedule a call with our team to explore the best secure communication setup for your needs.

%20%20(1).png)

.svg)
.svg)

.svg)
.svg)
