What Does Not Change
This does not change.
Most CISOs today report green on cryptographic security. But that “green” status is based on encryption standards with a published expiry date. NIST has set it. Adversaries are already exploiting the gap through harvest now, decrypt later strategies. The choice is a decision about what “secure” is allowed to mean on your watch.
Deploy a PQC-Hardened NodeDownload the CISO Quantum Harvest guide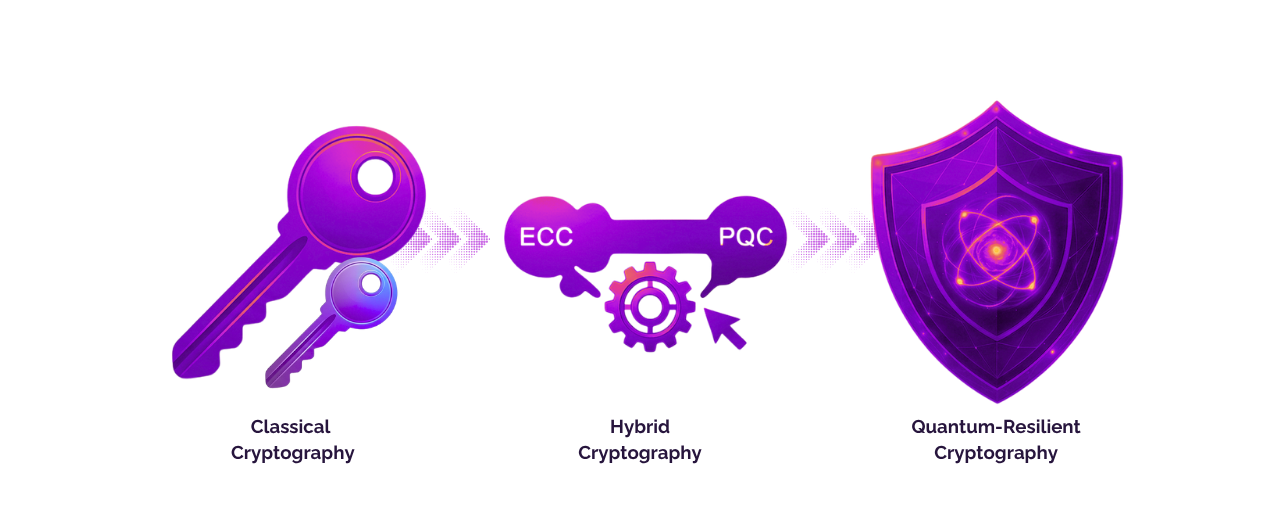
The organizations collecting your encrypted communications today are not waiting for physics. They already have what they need. Quantum computing will only be the decryption event. The collection event is happening now — and it will not appear in any of your current threat monitoring.


The security market is saturated with quantum-adjacent language. "Quantum-ready." "Quantum-resilient." "Future-proof encryption." None of these phrases have regulatory definitions. None of them commit a vendor to anything. There are only two questions that matter:

Read the Cryptographic Architecture Whitepaper →

We don't sell a future vision. We provide infrastructure that is operational today, within your specific jurisdiction, built on the standards that governments and businesses are already adopting.


The question every CISO asks before any infrastructure change is the same: what breaks? The answer here is straightforward.
Every day of delay is another day of communications being collected. The organizations that act now will have closed the window before it matters. The ones that wait will be explaining the breach — to their board, to regulators, and under a personal liability framework that did not exist five years ago.
Deploy a PQC-Hardened NodeSchedule a Sovereignty Readiness AssessmentDeployment timelines depend on your environment — on-premises, sovereign cloud, or Swiss cloud. For most organizations, the PQC-hardened stack deploys in the same timeframe as a standard RealTyme deployment. There is no extended migration period, no phased algorithm cutover, and no disruption to existing users. Your teams are on quantum-resistant infrastructure from day one of deployment, not at the end of a multi-year transition program.
No. RealTyme's hybrid PQC implementation is optimized specifically to avoid performance degradation in real-time communication. Post-quantum key establishment adds negligible overhead to session initiation. Once a session is established, all messages, calls, and file transfers run on AES-256 symmetric encryption — which is unaffected by quantum computing and unchanged by the PQC layer. Your teams will not notice a difference in speed, latency, or usability.
Post-quantum cryptography replaces mathematically vulnerable algorithms with new ones that quantum computers cannot break efficiently. It runs entirely on existing classical hardware and can be deployed across any network at any scale. Quantum Key Distribution uses quantum physics to detect eavesdroppers during key exchange — but requires dedicated optical fiber hardware and is currently limited to short-range, point-to-point links. PQC is the practical migration path for enterprise and government communication at scale. QKD is an additional layer for the most sensitive, fixed-infrastructure links where the hardware investment is justified.
No — and this is precisely the logic that creates HNDL exposure. The data being encrypted on your current platform today is the data at risk. Every month of delay between now and your platform refresh is another month of communications entering adversary archives under classical encryption. PQC migration does not need to wait for a platform refresh. RealTyme deploys as a sovereign, standalone infrastructure — it does not require replacing your existing stack first. The two can run in parallel during any transition.
Historical data encrypted under classical algorithms before your PQC deployment remains exposed to HNDL collection — this cannot be retroactively changed. That is precisely why the timing of migration matters. Data encrypted after deployment is protected by the hybrid PQC model. For organizations with highly sensitive historical archives, RealTyme's team can advise on re-encryption strategies for data at rest. The priority is stopping the growth of the vulnerable archive — which begins the moment you deploy.
Yes. The full PQC cryptographic stack — ML-KEM-1024 (FIPS 203) and ML-DSA-87 (FIPS 204) in a hybrid model with classical encryption — is available across all three hosting options. The deployment model does not affect the cryptographic architecture. Whether you deploy on your own infrastructure, in a sovereign cloud within your jurisdiction, or in the Swiss cloud, the mathematical protection is identical. What the deployment model determines is the legal jurisdiction governing your keys and data — which is the second half of the security equation.
The first step is understanding where classical cryptography is currently embedded across your stack — a Cryptographic Bill of Materials (CBOM). RealTyme's engineering team offers a Sovereignty Readiness Assessment that maps your current cryptographic exposure, identifies the highest-priority migration targets based on data longevity and sensitivity, and produces a documented transition plan. This assessment is the foundation of a defensible migration program — the kind that stands up to regulatory scrutiny and board review. Schedule one using the link below.
